
Dear
Sean
McCarthy,
09/24/2009
Welcome to the fifth edition of this newsletter -
it's a companion edition to my popular Compute This... newspaper column
in the Home Town News and I truly hope that you find it helpful.
Seminar update: 2 weeks ago I announced that I was thinking of
resurrecting
my old computer seminars. As of today (9/24/09) I have only  had
6 people respond in favor of the idea so that probably won't happen in
October as I had planned.
However,
on October 3rd. from about 10:00 am to about 2:00 pm I invite you to
join me at the Indian Sheriff's Dept. sub station in Vero Beach at the
Outlet Mall on 60 just west of 95 for our second Protect Your Identity Day!
I
was invited by D/S Roberta Hall of the Crime Prevention Unit to deliver
a presentation on identity theft. We did this in March and it was a
great success. We had a lot of fun!
Join us and learn how you can " Deter,
Detect, and Defend" against identity theft.
This
weeks newsletter was put together from reader comments and suggestions;
I rely on reader comments to figure out what to include in each
newsletter.
This week I had reader requests that I touch upon
"resizing images" (for you Steve!), on "how to know if that free
antivirus or spyware software is legit," "how to get into safe mode"
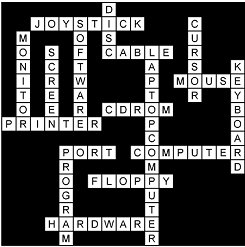
and Marianne asked me to include a list of "common computer terms."
Go ahead! Keep the comments and suggestions coming - I couldn't do this
with out you!
And as always I hope you enjoy this weeks newsletter.
Cheers!
Sean McCarthy |
|
Is that "free antivirus" offer really safe? |

Is it safe?
That is a question that everyone needs to ask before
downloading a piece of free anti-spy software that promises the world.
However, how does someone find out if something is safe before
installing some piece of garbage onto her machine?
You
could go by a friend's recommendation, "well so and so is running it
and they aren't having any problems so it must be safe." But maybe your
friend's machine is a wreck and he doesn't know it yet.
Some
people install software assuming it's safe just based on what that
software promises to do. It's an anti-spyware program, so it must be
safe, right?
Just because the software you are about to install
promises to keep you safe doesn't mean it doesn't come with its own bit
of nastiness.
Determining if a piece of software is safe, based
on what the download page promises, is one way many people are duped
into installing harmful stuff onto their machines.
In fact, one
of the most sinister ways spyware authors trick people into loading
their junk is by throwing a pop up window onto the screen warning users
that their "machine is already infected."
People fall for that all the time, only to find their machines infected
by something that they thought was going to help...
Continue reading
>>>> |
|
Safe mode? |
Computers,
just by the very their very complex nature, are prone to failure.
Ask anyone who has used a personal computer for any length of time, and
you will hear stories of system lockups, general protection
faults,
missing .dll, blue screen errors and even more cryptic messages. Most
of the error
messages that pop up are so technical in their wording that even
seasoned professionals have no idea what they mean. (Computer failure
is also the No. 1 reason why it's so very important to backup your
system; problems occur all the time, and without your data backed up,
you risk losing everything.)
Usually, a simple reboot will cure
system lockups and errors, but Windows also has built into it a tool
called "safe mode," which is specifically for troubleshooting and
correcting reoccurring problems. Perhaps you've seen it before; Windows
will sometimes boot up (load) into safe mode after a power failure or
an
improper shutdown to give you the opportunity to correct whatever
problem is going on. You can tell the system is in safe mode because
the resolution and color depth is reduced (the icons all look bigger
and the colors are all fuzzy) and the words "safe mode" appear in all
four corners.
But what is it for? What's the difference between
booting a machine in safe mode versus a normal startup, and how does
one get into safe mode deliberately?
Booting your computer in
safe mode allows Windows to load with only the essential items
necessary for the system to run. All of the "extra" stuff that loads on
startup is ignored, and just the core operating system loads. It does
this because nine out of 10 times, system problems are not caused by
the operating system itself but by items or programs that load after
Windows. By bringing the system up with minimal overhead, it makes
troubleshooting a finicky system all the more easier. In fact, often
all that is necessary to correct many problems is to bring the system
up in safe mode and then do a normal shutdown to let Windows clean
itself up and then boot normally.
When you click the Windows (Start)
button, then Shutdown, Windows goes through a bunch of "housekeeping"
chores that clean up its working environment, so the next time it boots
up there is not a bunch of stuff left over from its last session.
Temporary files (Windows' notes to itself), open files and running
processes all get closed during a normal system shutdown, meaning when
the system comes back up, it's not all cluttered with "yesterday's
stuff." That's why the system usually pauses a minute or two after you
click "Shutdown" and before it actually shuts down. It's also the
reason your system may boot up into
safe mode if you just hit the power button instead of doing a proper
shutdown - the system didn't have a chance to clean up after the last
session, so it may come up into safe mode to clean up.
But
cleaning up an improper shutdown is not all safe mode is for...
Continue reading
>>>>
|
10 computer terms that everyone should know
|
- Byte:
the standard size of data in a computer; 8-bits
- BIOS:
System that loads on boot up to prepare the machine so other software
can load, execute, and control the PC
- GB
(gigabyte): unit of information or computer storage equal to one
billion bytes
- OS
(operating system): interface between the application (word processor,
spreadsheet, etc.) and the computer hardware
- Firewall:
Hardware or a set of security policies to
screen incoming and outgoing messages
- FTP
(file transfer protocol): System used to transfer a
copy of a file from one computer to another computer with one acting as
client and the other as server
- CPU
(Central Processing Unit): the brain of the computer system where
calculations and decisions are made; also referred to as the processor
- Wireless
router: device that connects to your broadband internet service and
creates a "cloud of internet" that can be connected to wirelessly.
- Link:
Words, pictures or buttons on a web page that, when clicked, open
another page
- TCP/IP:
Communications protocols used for the Internet and other similar
networks. It is named from two of the most important protocols in it:
the Transmission Control Protocol (TCP) and the Internet Protocol (IP)
|
|
Thank you for reading. I hate
spam as much as anyone so please, if
you don't want to receive my newsletters, use the "SafeUnsubscribe"
link at the bottom of this email and you will be removed from my list.
I
also appreciate your feedback. Feel free to respond to this message
with any comments you may have and I promise to reply to you as soon as
possible.
An lastly, if you find my information helpful and you
overhear someone complaining about their computer, please mention my
name or forward this newsletter to them by clicking
here. Most of my business is referred to me by word of mouth
so without you I would not be in business. Thank you for your support.
Sincerely,
Sean McCarthy
"The Mouse Whisperer"
www.ComputeThisOnline.com
Sean@ComputeThisOnline.com
772-408-0680
888-752-9049
Ps. REMEMBER! If you forward this newsletter to a friend, use the
button or link above, not
the forward button in your email program!
|
|
|
 |
| Featured Article |

|
|
Re-size those pictures before
sending!
If you've ever received photos through e-mail, you may have run into
this weird phenomenon where the picture is so incredibly big all you
see is the top left hand corner of the picture and to see the rest you
have to scroll left and then down.
That's great if you want to
look at a close up of someone's nose (just scroll around till you find
it), but how do you "zoom out" so you can see the whole picture?
In order to do that, you have to take steps to save the picture then
re-open it with another program.
Today I thought I would cover why this happens and how to cope with it.
When
you open an e-mail and the picture is so big, it's important to keep in
mind that it's not your
fault. You aren't doing anything wrong at all.
Your e-mail program is working properly it's just a matter of "what you
see is what you get."
So what does that mean exactly? Well, quite
simply that means whoever sent you the picture didn't take the steps
(or didn't know how to take the steps) to "optimize the picture for
e-mail."
In English that means that whoever sent the e-mail
didn't take the time to shrink the picture first before sending it.
They likely just attached the picture as is to the e-mail and sent it
off.
So what do you do when you open an e-mail and the photo is
so big you have to scroll from side to side and up and down to see it
all? Wouldn't it be nice if your e-mail program automatically resized
the picture for you? Well, it would be nice, but unfortunately, it
doesn't.
What you have to do is save the picture to a folder on
your hard drive and then open it with some type of picture viewer to
see it in its entirety.
To do that (again, we're using Outlook
Express in this example, other e-mail clients like Windows Mail have
similar functions),
click on the little paper clip that represents the picture that's
attached to the e-mail and click "save as." That opens a standard "save
as dialogue box" where you select the folder you want to save in and
either change the name of the file or at least make a note of what it's
called...
Continue reading
>>>>
|
|
|